One of my pet peeves about logging into sites on my phone is the password field. On a large screen it makes sense that the field is obscured by * characters but what about on a small device only you can see?
I can’t be the only one bothered by this because the wifi login form on Android devices has a handy “Show password” setting. Maybe it’s because people use the default wifi password set by their ISPs so much it’s their only “strong” password. Anyway, I wished there was a similar setting for other login forms.
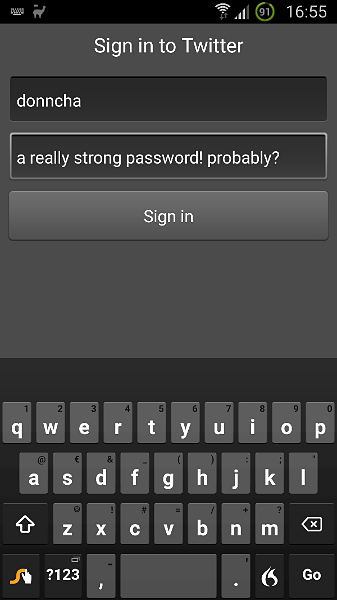
Well, now there is, sort of. A handy Xposed Framework module called HideNoPasswords that reveals the letters behind the dots. I found I could even swype my password which makes logging in with phrases so much easier.
There are downsides. Security is the most obvious one. An application could take screenshots in the background when it detects the keyboard is in use and send that data somewhere. Someone could look over your shoulder and see the password.
Also, your phone has to be rooted, and you need the Xposed Framework installed but if you’ve conquered those hurdles installing this module is simple.
Here’s the XDA Thread on the module, and the XDA blog post where I found out about this handy extension.

